Every minute, someone falls victim to identity theft in the American marketplace, making digital safety a top priority for young professionals everywhere. As daily life grows more connected, the risk of personal data being intercepted through RFID technology is higher than ever. This guide helps you navigate the world of modern RFID protection, spotlighting essential facts, technology basics, and stylish options that align with your fast-paced urban lifestyle.
Table of Contents
- Defining Rfid Technology And Protection Basics
- How Rfid Works In Everyday Life
- Types Of Rfid-Blocking Accessories Explained
- Risks Of Rfid Skimming And Data Theft
- Common Mistakes In Choosing Rfid Protection
Key Takeaways
| Point | Details |
|---|---|
| Understanding RFID Technology | RFID technology uses electromagnetic fields for automatic identification and tracking, consisting of tags, readers, and backend systems. |
| Types of RFID Tags | Passive tags draw power from readers while active tags have their own power source, affecting their range and usage. |
| RFID Privacy Risks | RFID skimming can lead to unauthorized access and identity theft; using RFID-blocking accessories is essential for protection. |
| Choosing Effective Protection | Not all RFID-blocking products provide equal protection; consumers should assess materials and technologies for reliable security. |
Defining RFID Technology and Protection Basics
RFID technology represents an advanced wireless communication method that enables automatic object identification and tracking through radio waves. Radio frequency identification systems use electromagnetic fields to transmit data between special tags and readers without requiring direct physical contact. This technology allows for seamless, contactless data exchange across multiple industries and applications.
At its core, an RFID system consists of three primary components: a tag, a reader, and a backend system. The RFID tag contains a microchip and antenna that stores unique identification information. When an RFID reader generates an electromagnetic signal, passive tags draw power from this signal, enabling them to broadcast their stored data. Active tags, in contrast, have their own internal power source and can transmit signals over longer distances.
Here’s a quick comparison of passive and active RFID tags:
| Attribute | Passive RFID Tags | Active RFID Tags |
|---|---|---|
| Power Source | Reads power from signal | Battery-powered |
| Transmission Distance | Short range (up to 10 ft/3 m) | Long range (up to 300 ft/90 m) |
| Typical Use Cases | Inventory, retail, IDs | Asset tracking, logistics |
| Maintenance Needs | Maintenance-free | Requires battery replacements |
The versatility of RFID technology makes it applicable in numerous sectors, from inventory management to security protocols. Automatic identification technologies enable tracking assets in supply chains, pharmaceutical distribution, retail environments, and even animal identification systems. However, this convenience also introduces potential privacy risks, as unauthorized readers could potentially intercept personal information stored on these tags.
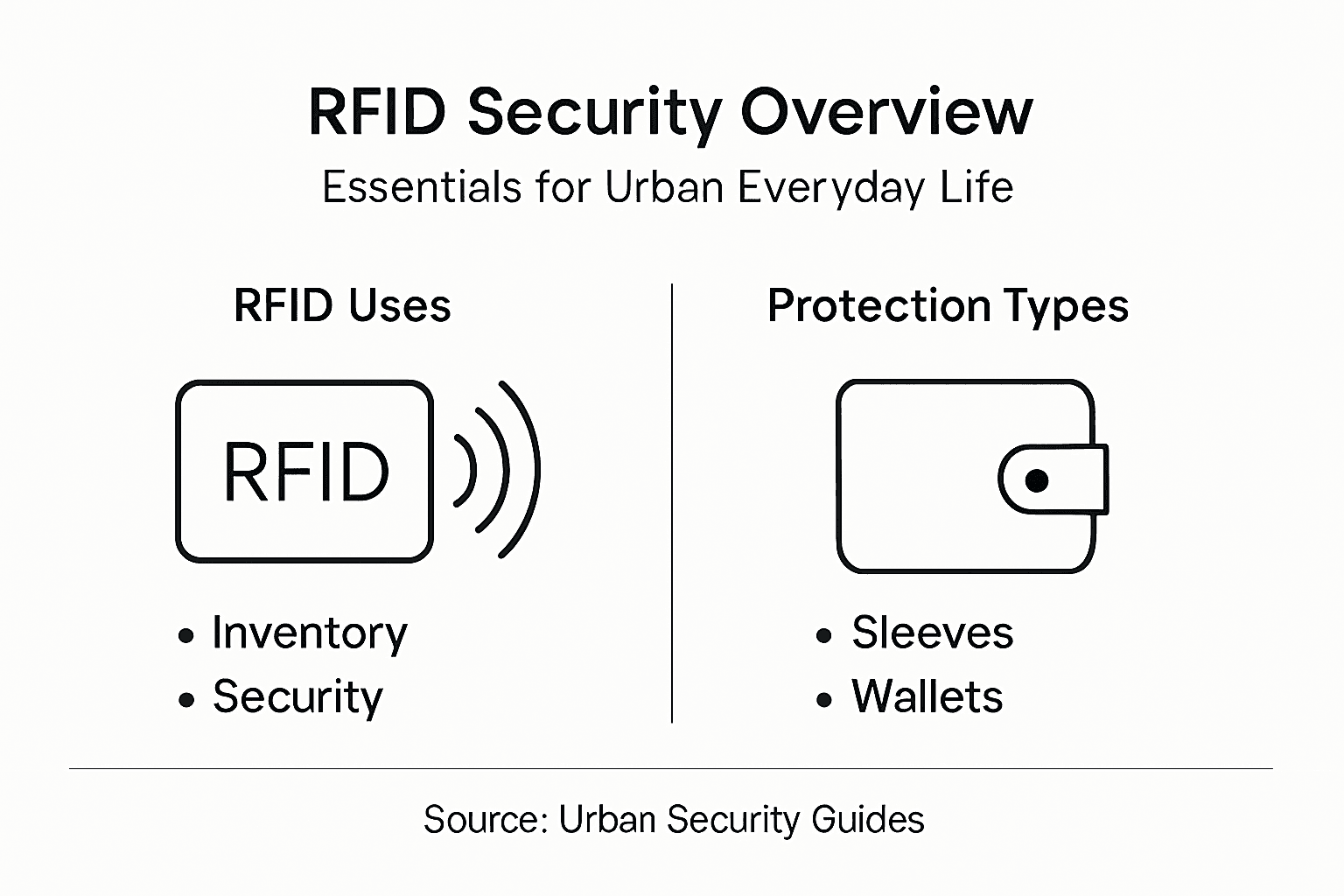
Pro tip: Invest in RFID-blocking accessories like wallets or phone cases to prevent unauthorized scanning of your personal identification and payment cards.
How RFID Works in Everyday Life
RFID technology has seamlessly integrated into numerous aspects of urban life, transforming how we interact with everyday objects and systems. Advanced tracking technologies enable automatic identification and data capture across multiple sectors, making our daily experiences more efficient and connected. From retail shopping to public transportation, RFID chips silently work in the background to streamline processes and enhance user experiences.
In retail environments, RFID tags help manage inventory with unprecedented precision. Stores can track product movement, prevent theft, and optimize stock levels by embedding tiny chips in merchandise. Similarly, access control systems in offices, apartments, and secure facilities use RFID-enabled cards to grant entry, replacing traditional keys with more flexible and trackable solutions. Public transit systems have also adopted this technology, allowing commuters to tap cards or smartphones for seamless travel across cities.
Radio frequency identification systems extend far beyond commercial applications. Healthcare facilities use RFID to track medical equipment, monitor patient records, and ensure accurate medication dispensing. Logistics companies leverage these chips to track shipments globally, providing real-time updates on package locations and conditions. Even personal items like passports, credit cards, and event tickets now incorporate RFID technology to enhance security and convenience.
Pro tip: Periodically check your personal items for RFID-enabled documents and consider using protective sleeves to prevent unauthorized scanning of sensitive information.
Types of RFID-Blocking Accessories Explained
RFID-blocking accessories have evolved from simple protective sleeves to sophisticated fashion-forward solutions that seamlessly integrate security into everyday items. Privacy protection technologies utilize specialized materials like metalized fabrics and aluminum layers to create effective barriers against unauthorized digital scanning. These innovative accessories function as personal security shields, preventing potential electronic pickpocketing and data theft.
The most common RFID-blocking accessories include wallets, passport holders, card sleeves, and specialized backpacks. Wallet designs range from minimalist metal-infused leather options to full-featured multi-compartment models that block signals from credit cards, government IDs, and contactless payment cards. Some advanced accessories incorporate additional features like smartphone charging capabilities or built-in tracking systems, transforming traditional protective gear into multifunctional urban survival tools.

RFID-blocking wallet designs cater to different lifestyle needs, offering variations for travelers, professionals, and everyday consumers. Travelers might prefer compact passport wallets with multiple signal-blocking compartments, while urban professionals might opt for sleek, slim card holders that integrate seamlessly with business attire. The key is finding a balance between comprehensive protection and personal style, ensuring that security doesn’t compromise aesthetic preferences.
The table below summarizes common RFID-blocking accessories and their typical features:
| Accessory Type | Main Features | Ideal User | Added Benefits |
|---|---|---|---|
| Wallet | Metal lining, multi-slots | Professionals, travelers | Protects multiple card types |
| Passport Holder | Signal-blocking layers | International travelers | Stores travel documents safely |
| Card Sleeve | Individual card protection | Everyday consumers | Lightweight, portable |
| Backpack | Hidden shielded pocket | Urban commuters | Secures devices on the go |
Pro tip: Test your RFID-blocking accessory periodically by attempting to scan your cards near a contactless reader to confirm its continued effectiveness.
Risks of RFID Skimming and Data Theft
RFID skimming represents a growing digital threat that transforms everyday technology into a potential security vulnerability. Unauthorized data capture techniques enable criminals to wirelessly extract sensitive information from contactless cards, passports, and electronic devices without physical contact or immediate detection. Modern urban professionals are particularly susceptible, carrying multiple RFID-enabled devices that broadcast personal data continuously.
Criminals employ sophisticated methods to exploit RFID technology’s inherent vulnerabilities. They can use concealed readers in public spaces like coffee shops, transit systems, or crowded streets to intercept signals from credit cards, government identification, and electronic passes. RFID skimming strategies often involve disguising scanning equipment as everyday objects, making detection nearly impossible for unsuspecting victims. The stolen data can be quickly used for fraudulent online purchases, identity theft, or sold on underground digital marketplaces.
The financial and personal risks associated with RFID skimming extend beyond immediate monetary losses. Victims might face long-term consequences like damaged credit scores, legal complications, and extensive time spent recovering their digital identity. Some RFID-enabled technologies have improved encryption, but many older cards and systems remain vulnerable to sophisticated scanning techniques that can capture data from surprising distances.
Pro tip: Maintain a rotating schedule of monitoring your financial statements and consider using RFID-blocking accessories in high-traffic public areas to minimize potential data interception risks.
Common Mistakes in Choosing RFID Protection
Urban professionals often make critical errors when selecting RFID protection, undermining their personal security strategy. Comprehensive security approaches require more than simply purchasing a wallet with RFID-blocking claims. Many consumers mistakenly assume all protective accessories offer equal levels of protection, overlooking crucial details about signal blocking effectiveness, material quality, and technological sophistication.
One prevalent mistake involves choosing RFID-blocking products based solely on aesthetic appeal or price point, rather than evaluating their actual protective capabilities. Not all RFID blockers are created equal. Some budget-friendly options provide minimal protection, creating a false sense of security. Professionals should investigate the specific shielding technologies, understand the materials used, and verify the product’s ability to block multiple frequency ranges typically used in contactless cards and electronic identification.
Privacy protection strategies demand a holistic approach that extends beyond physical accessories. Consumers frequently neglect complementary security measures like periodically monitoring financial statements, using virtual credit card numbers, and understanding the limitations of their protection methods. The most effective RFID security combines technological solutions with personal vigilance and an understanding of potential digital vulnerabilities.
Pro tip: Request technical specifications from RFID-blocking product manufacturers and conduct your own signal blocking tests using a contactless card and an RFID reader to verify actual protection levels.
Upgrade Your Security with Stylish RFID Protection
The article highlights the growing risk of unauthorized RFID scans that threaten your personal and financial information in everyday urban life. If you want to avoid common mistakes like relying on ineffective protection or ignoring key vulnerabilities, it is crucial to choose accessories that combine real RFID-blocking technology with modern style. The pain of potential identity theft or data skimming can be eliminated by using proven solutions designed specifically to block unwanted electronic access.
Discover the difference at InvisiTechWear, where technology meets fashion. Our curated collection of RFID-blocking wallets & bags – Daon Tech provides innovative materials that shield your cards from digital pickpockets without sacrificing your personal style.
Protect your sensitive information today with accessories that work as hard as you do. Browse our selection at InvisiTechWear now and enjoy peace of mind knowing your data is secure wherever urban life takes you.
Frequently Asked Questions
What is RFID technology and how does it work?
RFID (Radio Frequency Identification) technology uses electromagnetic fields to automatically identify and track tags attached to objects. An RFID system consists of tags, readers, and a backend system, enabling contactless data exchange.
What types of RFID tags exist and what are their differences?
There are two main types of RFID tags: passive and active. Passive tags draw power from the reader’s electromagnetic signal for short-range communication, while active tags have their own battery, allowing for longer-range communication.
How can I protect my personal information from RFID skimming?
To protect against RFID skimming, invest in RFID-blocking accessories like wallets, passport holders, or card sleeves, which prevent unauthorized scanning of sensitive data. Regularly monitor your financial statements and use virtual credit cards where possible for added security.
What should I consider when choosing RFID-blocking products?
When selecting RFID-blocking products, evaluate their materials, shielding technology, and protective capabilities. Not all products are the same; some may offer only minimal protection, so it’s important to research manufacturers and verify specifications.




